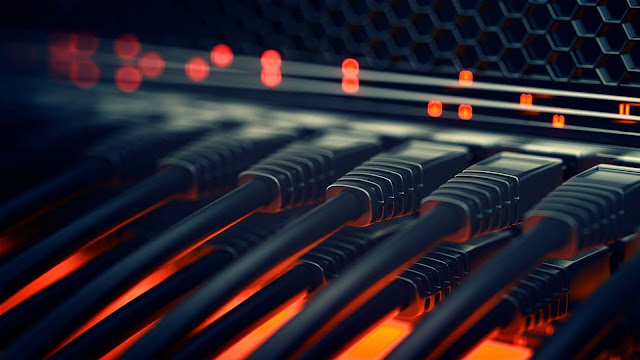
Speed Test By Networkings Academy
User Friendly Speed Test Internet Speed Test 0.00 Mbps Start Test Idle Client Info IP: - ISP: - Country: - Ping - ms Download - Mbps Upload - Mbps